In this article, we will show you how to add user to sudo group on Debian 11 and provide sudo access to an existing user. The sudo command is the preferred means to handle elevated permissions. In supported versions of Debian, using the sudo command will grant the permissions for 15 minutes.
Standard user accounts are restricted from performing sensitive tasks, such as viewing the contents of the /root directory. This prevents the accidental use of commands with massive consequences. It also makes it more difficult for intruders to compromise a system. However, sometimes you need to run an administrative command. Sudo – or Super User Do – grants you privileges to run sensitive tasks.
Prerequisites
- A system running a supported version of Debian
- Access to a root user account or another account with sudo privileges
- An user account without sudo privileges
Switch to root Account
If you have a fresh installation then you have to login or switch the user to root. So you can use the following command to switch the user account to root.
$ su -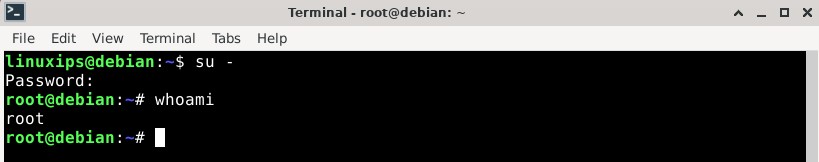
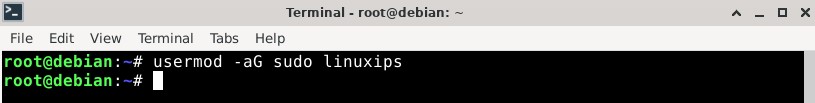
Add User to Sudo Group
Most Linux systems, including Debian, have a user group for sudo users. To grant the new user elevated privileges, add them to the sudo group.
In a terminal, enter the following command (root user):
# usermod -aG sudo usernameReplace the username with your username.
Again, if you are login with sudo privileges account, run the command with sudo as follows:
$ sudo usermod -aG sudo newuserThe -aG option tells the system to append the user to the specified group. (The -a option is only used with G.)
Verify User Belongs to Sudo Group
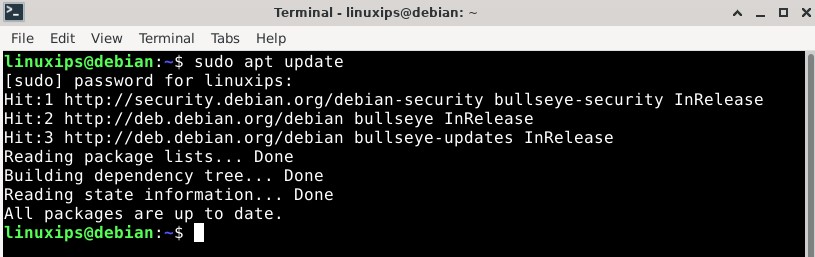
Now after login to Debian 11 again you have to simply run the following command to verify that you have sudo privilege:
$ sudo apt update Conclusion
Conclusion
Now you know how to give sudo privileges to the user on Debian 11 or you can say how To add a user to the Sudo group on Debian 11. Before sudo, users would log in to their systems with full permissions over the entire system with the su command. The sudo command in Linux strikes a balance – protecting user accounts from malicious and inadvertent damage while allowing a privileged user to run administrative tasks.

 Conclusion
Conclusion